
Denial of Service Attack (DOS) is an attack against PC or system which decrease, confine or prevent the availability of its framework sources for approved clients.
Know more about DOS by Linux Online Training1.Denial of Service Attack:
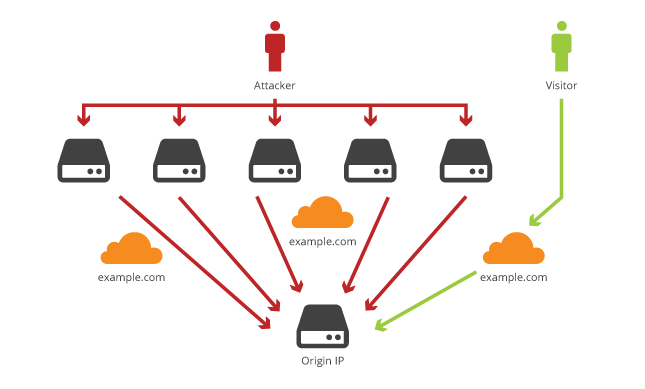
It is a type of attack where many undermined frameworks all the while attacking a single framework, accordingly causing a DOS attack for the clients of the target computer.
An attacker can choose the Zombies and once programmed, he sets up an order and controller to control the zombies that attack the target computer. A bot is a Virus programming introduced on optimized machines. This gives the attacker authority over the zombies. The system of Bots called a botnet.
2.Types in DOS:
a)Volumetric attacks:
With this attack, the whole transmission capacity of a system is expended so the approved customers won't have the option to get the assets. This is received by flooding the system gadgets like centre points or switches.
With various ICMP echo demand/answer sets. So the whole transmission capacity is expended, and no different customers can associate with the target Linux PC.
b)Syn flooding:
It is the next attack where an attacker bargains so many zombies and all the while floods the goal with various SYN sets. The objective will be over-powered by the SYN demands, it is possible that it goes down or it shows it decreased in a continuous way.
c)Fragmentation attacks:
This is an attack that battles against the re-joining capacity of the Goal. Various divided sets sent to the objective, making it hard for the objective to re-assemble them with these lines, avoiding access to the approved users.
d)TCP-State exhaustion attack:
The attacker initiates up and tears down TCP links and over-powers the steady tables accordingly, causing a DOS attack.
e)Application Layer Attacks:
The attacker benefits the programming Errors and bugs, in the app to cause the denial of service attack. It received by sending various app requests to the goal to send the goal needs so it won't have the option to guide any valid users.
A programming mistake on account of buffer overflow attack, If the memory assigns to a variable is smaller than the needed one, at that point it might prompt memory leakage or crashing the whole app.
f)Plashing:
Generally, it finished by making permanent harm to the framework equipment. By sending false updates to the equipment along these lines making them totally unusable. The main plan is to re-start the tools.
3.Counter Measures:
1. Use Updated Anti-virus apps.
2. Check the network for the risk of a DOS attack.
3.Close unwanted controls in the main system.
4. Discover and avoid handlers. Secure optional systems.
5. Perform exact action profiling and In-Out sifting to channel through unknown traffic.
6. Use inside and out set Analysis.
7. Use top defence-in-depth terms.
8. Add extra load balancers to get traffic and set up logic to control traffic.
9.Correct program errors and bugs.
10. Use Strong encryption systems.
4.Distributed Denial of Service Attack:
A Distributed Denial of Service (DDoS) attack uses many infected gadgets and links spread far and wide as a botnet. A botnet is a single device that has been ruin by cyber-criminals without the data on the owners of the Devices.
The programmers infect PCs with virus programming, to get the frame to send spam and fake bits to variant gadgets and servers. A goal server that falls to a DDoS attack will brush an overload because of the hundreds of fake traffic that comes in.
Since the server attacked from many sources, mark every one of them, that send from these sources may trouble. Additionally, server traffic from fake traffic may be tough to do. Consequently, another drive behind why it is tough for a server to take a DDoS attack.
A DDoS attack can use as an automatic production network attack. In the event that the cyber attackers can't penetrate the security frame of various goal sites. They can locate a weak link. With every one of the goals and attacks the Internet. At the point when the connection optimized. The main targets would affect in an Indirect way.
Finally, these are the best-known facts about, denial of service attack in upcoming days we will update more Data on this Topic.